Documentation Index
Fetch the complete documentation index at: https://docs.adcontextprotocol.org/llms.txt
Use this file to discover all available pages before exploring further.
Experimental. TMP is part of AdCP 3.0 as an experimental surface — it may change between 3.x releases with at least 6 weeks’ notice. Sellers implementing TMP MUST declare
trusted_match.core in experimental_features. See experimental status for the full contract.Step 1: The problem — wasted budget
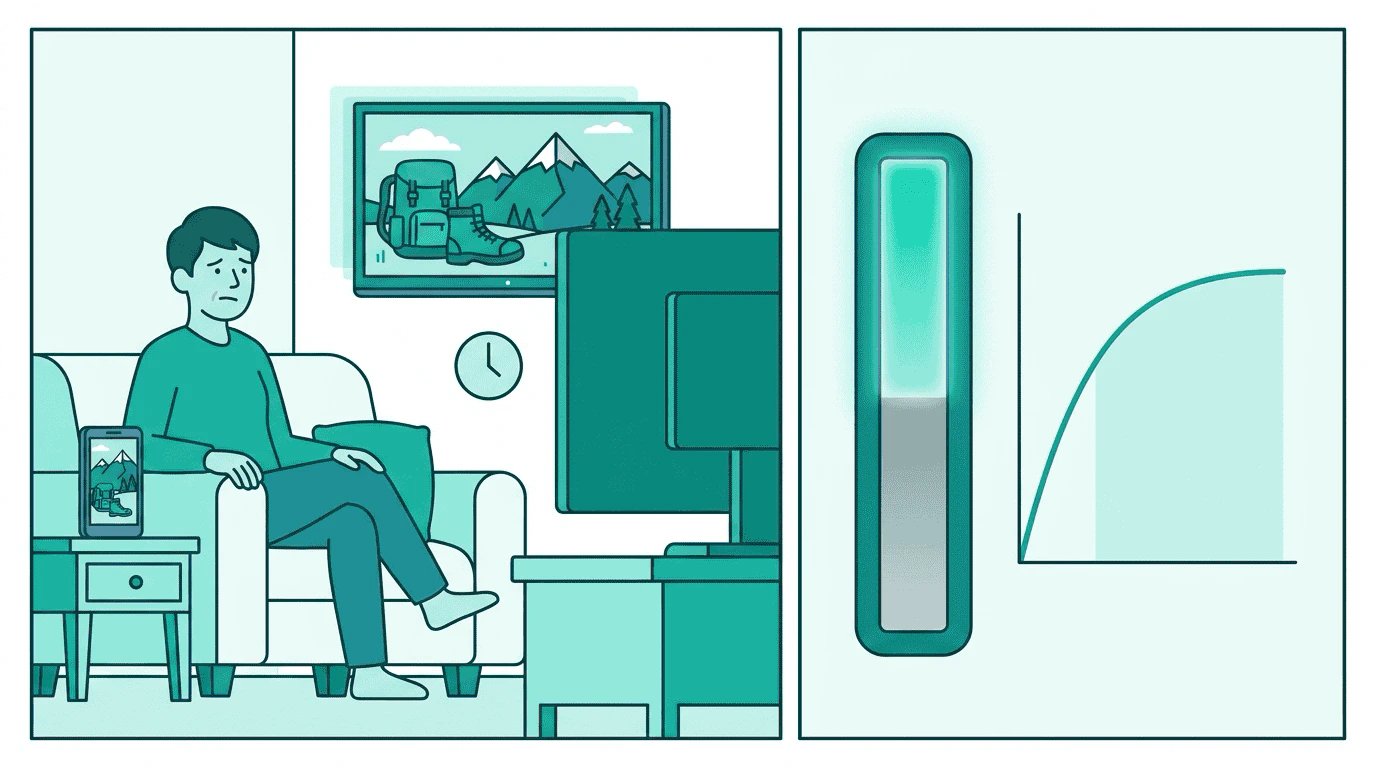
StreamHaus, OutdoorNet, and PodTrail each count independently. A viewer who watches hiking content on StreamHaus after dinner, then browses OutdoorNet on their phone 30 minutes later, gets the same ad again — well inside the 2-hour recency window Sam set. Multiply across a week and the viewer gets 15 impressions instead of 5, concentrated instead of spaced:| Publisher | Impressions counted | Actual viewer experience |
|---|---|---|
| StreamHaus | 5 (within cap) | Same ad every session |
| OutdoorNet | 5 (within cap) | Same ad every session |
| PodTrail | 5 (within cap) | Same ad every session |
| Total | 15 | 3x over Sam’s cap |
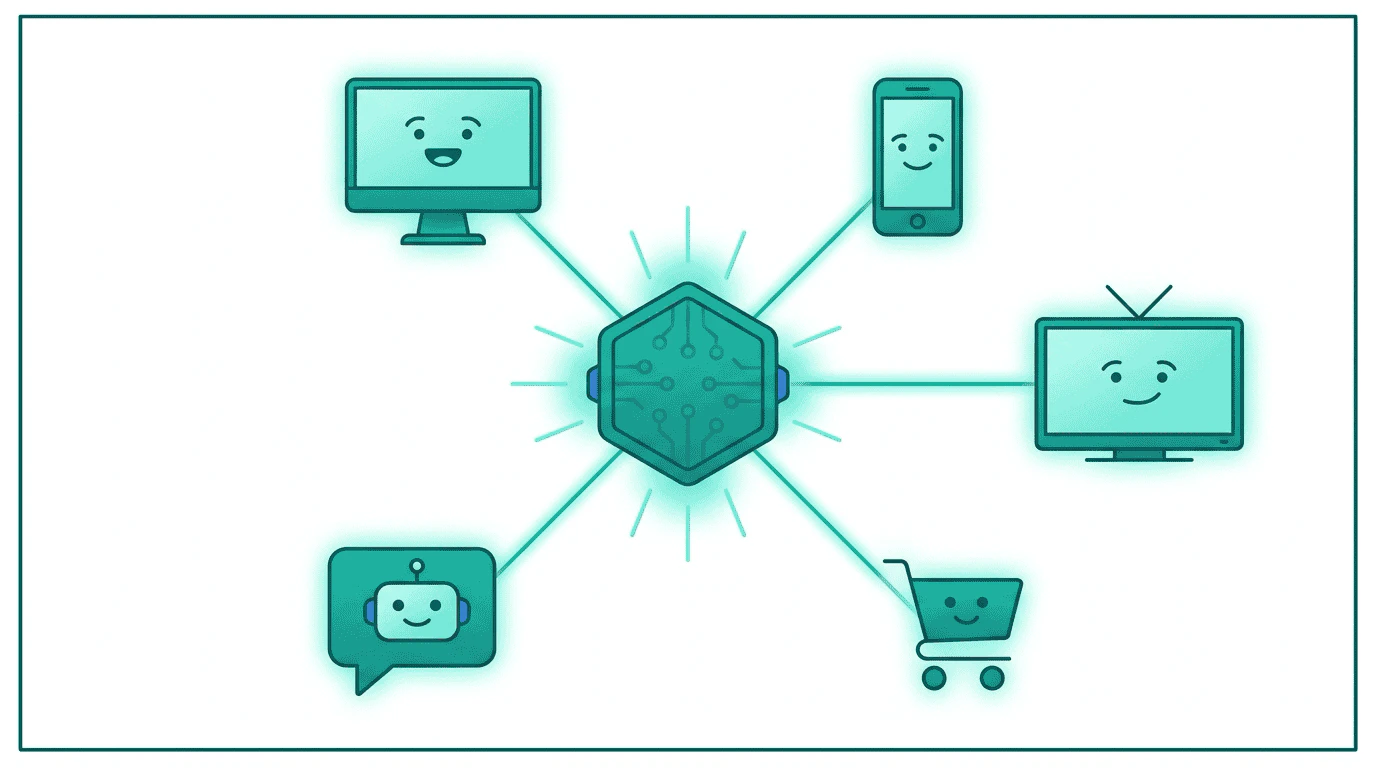
Step 2: Adding the TMP Router
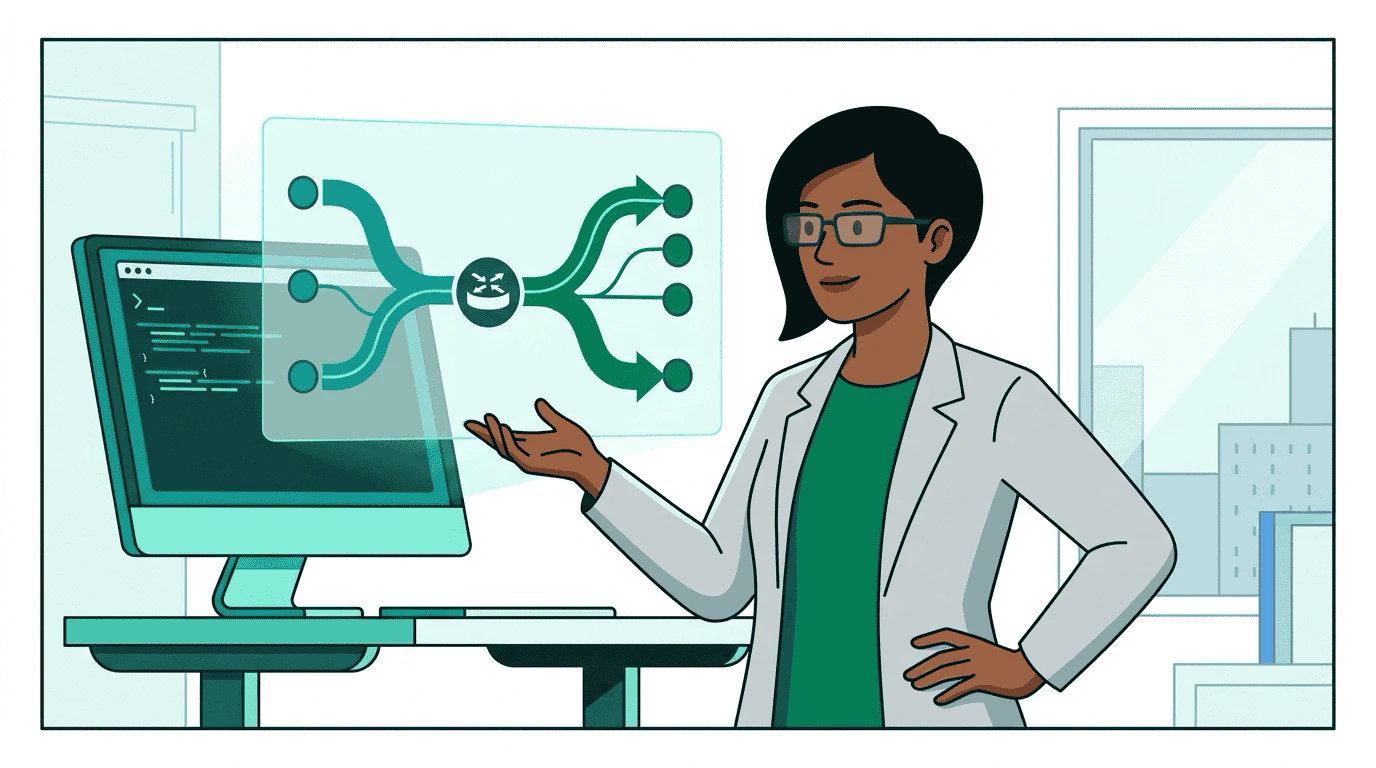
What Priya configures
What Priya configures
Priya registers Sam’s buyer agent (Pinnacle) as a TMP provider on the router:
context_match: true means the router sends content context to Pinnacle for targeting. identity_match: true means it also sends opaque user tokens so Pinnacle can enforce frequency caps and audience eligibility. properties scopes which StreamHaus properties this provider serves — Pinnacle evaluates web and iOS, not CTV. latency_budget_ms sets a per-provider timeout; if Pinnacle consistently exceeds it, the router deprioritizes it.The router fans out to all configured providers in parallel and merges their responses.Step 3: Context Match — what’s on the page?
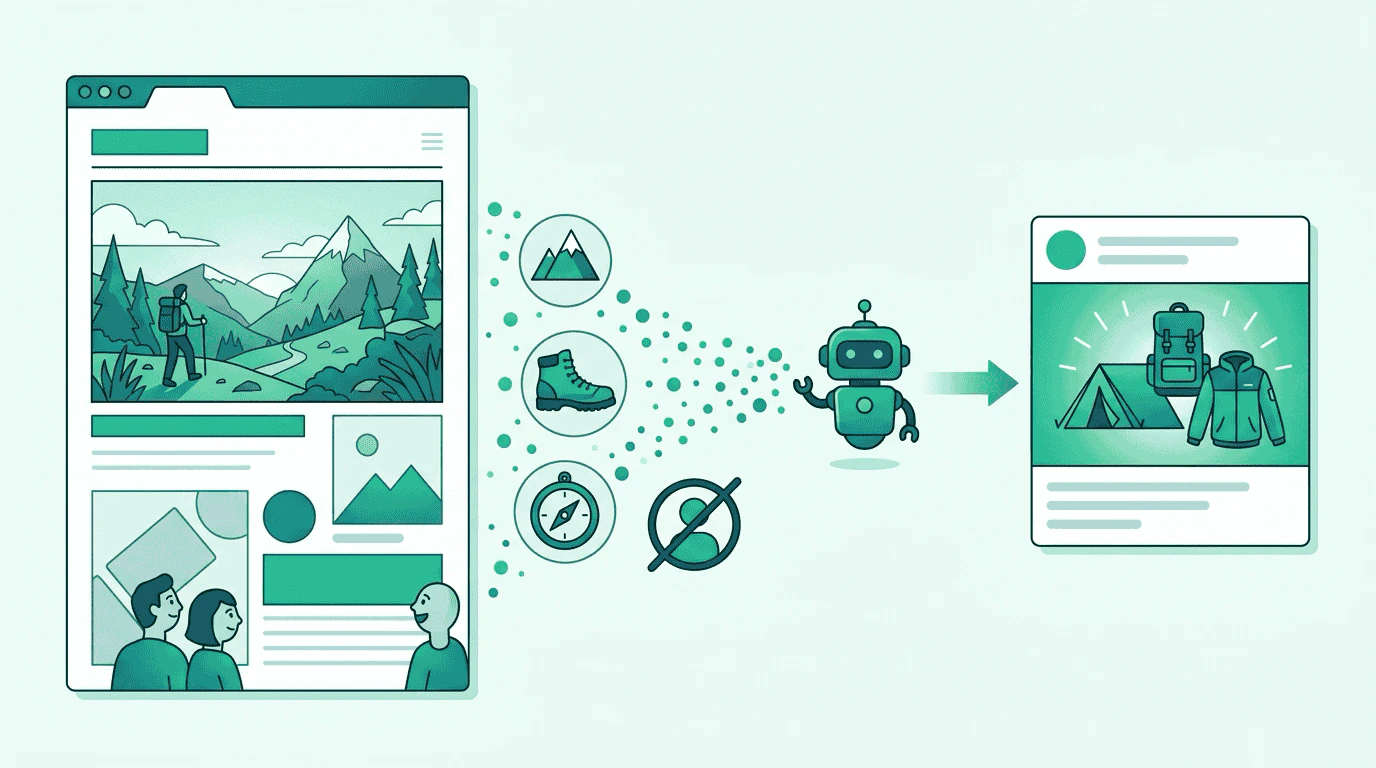
property_rid identifiers, so the buyer knows exactly which property this request came from. StreamHaus sends a Context Match request with the article’s content signals, placement, and geo.
Sam’s buyer agent evaluates: “This hiking content matches pkg-outdoor-display.” It responds with an offer that includes a creative manifest — the Trail Pro 3000 banner.
The key constraint: no user identity crosses this boundary. The buyer evaluates content, not people. It doesn’t know who is reading the article — only what the article is about.
Context Match request and response
Context Match request and response
Request from StreamHaus to Sam’s buyer agent:The publisher sends both
artifact_refs (for buyers that crawl content directly) and context_signals (pre-classified topics and keywords as a fallback). The buyer agent already knows which packages are active for this placement — it set them up via create_media_buy. No package list needs to travel on the wire.Response from Sam’s buyer agent:Step 4: Identity Match — is this user eligible?
Identity Match request and response
Identity Match request and response
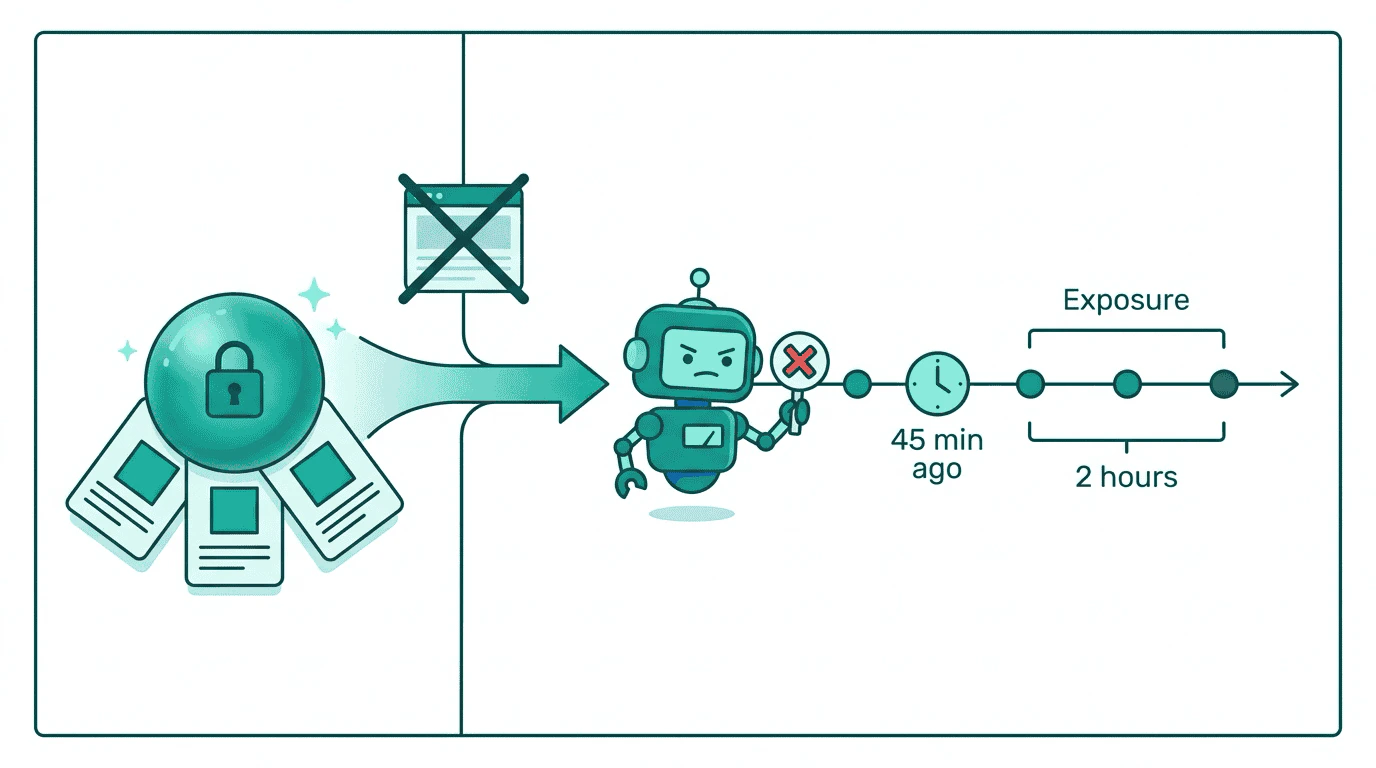
Request from StreamHaus to Sam’s buyer agent:Response from Sam’s buyer agent:Only eligible packages are listed —
pkg-outdoor-audio passes the buyer’s checks. The serve_window_sec: 60 tells the router to cache this eligibility for 60 seconds.The example sends package_ids explicitly, but the publisher MAY omit it — Sam’s identity-match service resolves the active package set from seller_agent_url. When package_ids IS sent, its composition MUST be independent of the current page — either all-active (every Sam package at StreamHaus) or fuzzed (a random sample padded with synthetic IDs that Sam will silently drop). A page-specific subset is forbidden; it would let the buyer correlate package sets across Context Match and Identity Match, breaking the structural separation.Step 5: The join — StreamHaus makes the decision

- Context Match said: “Activate
pkg-outdoor-displaywith this creative manifest.” - Identity Match said: “Not eligible — recency window.”
Step 6: Three winners

| Before TMP | With TMP |
|---|---|
| Each publisher counts independently | Buyer agent tracks exposure across all publishers |
| 15 impressions per viewer per week | 5 impressions per viewer per week, properly spaced |
| Budget buys frequency | Budget buys reach |
| Concentrated repetition, ad fatigue | Spaced exposure, higher effectiveness per impression |
| Publishers compete on volume | Publishers compete on quality and buyer experience |
Step 7: Same protocol, every surface
Go deeper
AI assistant mediation
A mediation protocol for AI assistants — how demand finds conversational AI when the context can’t be broadcast.
The execution gap
Why existing protocols fail at serve time and why TMP takes a matching approach instead of an auction approach.
Context and identity
Both operations with concrete examples, including catalog refinement and the publisher-side join.
Specification
Authoritative message types, field tables, and conformance requirements.
Privacy architecture
Structural separation, temporal decorrelation, and TEE attestation.
Data protection roles
Controller vs. processor analysis for each TMP participant.
Router architecture
Deployment, fan-out, and provider configuration.